Many organisations don’t need a brand-new business continuity plan. They need a refresh that makes the plan credible again: practical scope, clear ownership, scenario-ready runbooks, and evidence that it works under pressure.
If your BCP feels like an archive document rather than a lifeline, people will ditch it when it matters. That’s not a theory problem, it’s a trust problem. When disruption hits, decision-makers will either respond as planned or default to luck and experience — and once they deviate, you’re into untested territory.
This guide shows how to refresh an existing plan in 2026 in a way that exposes real gaps, tightens response and recovery, and produces assurance stakeholders can rely on.
For buyers writing a scope of work, you might also find this useful: 10 deliverables to include in a BCP refresh scope of work so the outcome is incident‑ready.
What “refresh” means (and what it doesn’t)
A refresh is not “rewrite the document and re-issue it”.
A refresh is a defined piece of work that restores three things:
- content that reflects the business as it is now (not a year ago)
- capability: people can actually use it and know what to do
- control: governance, sign-off, maintenance and continual improvement
If the refresh doesn’t improve those, it’s just formatting.
The three reasons plans get ignored in real incidents
When a plan gets ditched mid‑incident it’s usually one of these:
- denial: senior people weren’t involved enough and don’t trust what’s in it
- obsolescence: the organisation changed faster than the plan did
- distrust: it hasn’t been shown to work, or it’s never been exercised properly
A good refresh is designed to remove those failure modes, not to “tick the review box”.
Step 1 — Define a practical scope of work (so the refresh finishes)
You can’t refresh “everything” without creating a programme that never ends.
A sensible scope anchors on what you already stress across your process content: recover critical value streams within acceptable deadlines, based on dependencies and impacts.
A simple scope rule that works
Refresh what directly affects your ability to:
- respond quickly to a major disruption
- recover the most critical work first
- meet time pressures that matter (your real “pace of recovery”)
Scope template (copy/paste)
Use this exact structure in your project brief:
- Purpose of refresh: (assurance / incident learning / ISO alignment / tender or stakeholder requirement)
- In scope services / value streams: (top X critical services, not every process)
- Recovery expectations: (what “acceptable deadlines” look like and what you must protect first)
- Scenarios in scope: (the disruption types you will actually test)
- Locations / teams: (only those supporting in-scope services)
- Dependencies in scope: (people, premises, IT, suppliers, data)
- Deliverables: (updated runbooks, role cards, contacts governance, exercise evidence, actions backlog)
- What is explicitly out of scope: (so you don’t drift)
That one “out of scope” line prevents 50% of refresh programmes from failing.
Step 2 — Run a gap assessment that focuses on usability (not maturity theatre)
Most gap assessments produce a maturity score and a long list of “recommendations”. They don’t tell you what will break on day one of an incident.
Your own writing repeatedly comes back to one question: “does it work?”
So the gap assessment should be structured around:
- can someone find the right response guidance fast enough?
- do roles have clear tasks, authority and escalation?
- are recovery deadlines and priorities still credible?
- would the plan survive the “messy middle” of an incident, not just the tidy beginning and end? (this is exactly why exercising matters)
Practical output
A one-page prioritised gap list with:
That last line (how you prove it) is where refreshes move beyond box-ticking.
Step 3 — Revalidate impact, deadlines and dependencies (don’t refresh plans on stale assumptions)
Plans become unusable when the business changes but the assumptions don’t.
Your process content is explicit: you need to understand what really matters and how fast you must recover; your approach models the business from a resilience standpoint and maps dependencies and impacts.
So in a refresh you don’t necessarily need a full BIA rebuild — but you do need a structured revalidation of:
- critical services / value streams (still correct?)
- recovery deadlines (still realistic?)
- dependencies (what has changed in IT/SaaS, suppliers, data flows, remote working?)
If you skip this, you’ll “refresh” the document and keep the wrong recovery plan.
Step 4 — Replace monolithic plans with scenario runbooks (the biggest practical win)
A common reason plans fail is that they’re monolithic and slow to use: lots of pages, cross-referencing, people printing and annotating sections, versions drifting and the team leader carrying the whole cognitive load.
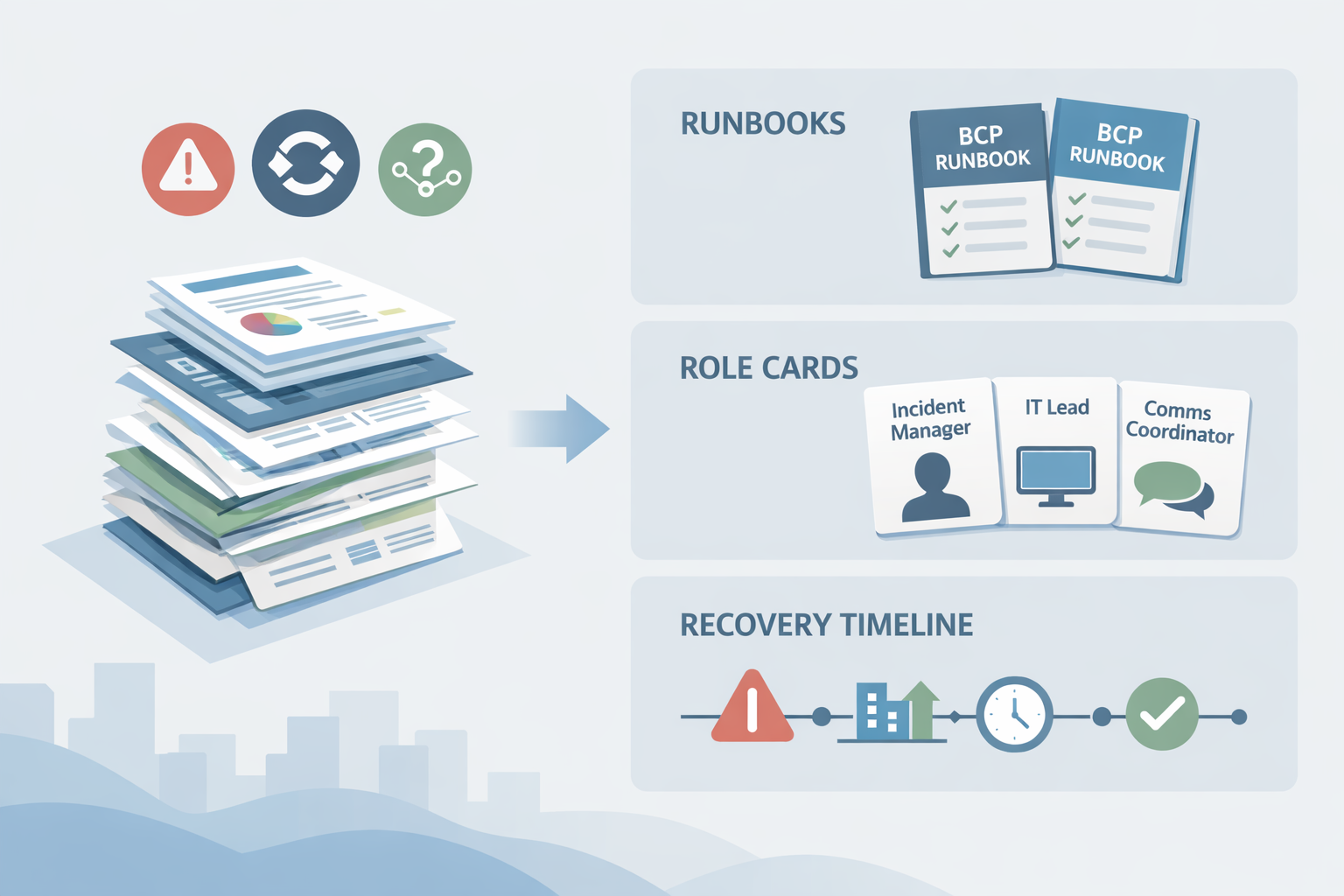
Your approach is the opposite: one concise runbook per scenario, backed by role cards, so teams can act quickly without wading through the entire BCP.
What to refresh, specifically
For each in-scope scenario, your refresh work should produce:
- a concise runbook that defines what must be done, in sequence, against deadlines
- role cards that sit alongside the runbook and task each assignee specifically for that scenario
- a single published timeline so activity tracking doesn’t splinter into multiple private notes
That is exactly how you move from “plan exists” to “plan is usable”.
Step 5 — Fix roles and contact governance (because this is what breaks first)
In a real disruption, delays often come from uncertainty:
- who is leading?
- who decides?
- who escalates?
- who is the deputy?
- who has the latest contact details?
Your own emphasis on role cards, plus your focus on organised response (incident/crisis/recovery integration), points to the same thing: response structure must be pre-agreed if chaos is to be avoided.
A 2026 refresh should include contact governance
Not just “a list of contacts”, but rules for keeping it current:
- where it lives
- who owns updates
- how often it’s reviewed
- how it’s accessed during disruption
This is one of the simplest changes that materially increases readiness.
Step 6 — Prove readiness with tabletop exercises (and capture evidence properly)
Plans don’t become trusted because they’re well written. They become trusted because they’re practised.
Your crisis simulation page describes a clean progression:
- familiarise (training)
- build confidence (tabletop exercises stepping through the planned response)
- challenge (simulation with deadlines, mistakes, rewind/replay)
- improve (log, analyse and report on every exercise)
That’s the right mindset for a refresh: exercise is not “afterwards”; it’s part of the work and a source of gap discovery.
What the refresh exercise should test
Make exercises explicitly target the refresh outcomes:
- runbook clarity under time pressure
- role interactions and information flow between incident, crisis and operational teams
- whether recovery sequencing matches dependency reality
What “evidence stakeholders trust” looks like
Not minutes that say “exercise completed”, but artefacts that show capability:
- scenario objectives and success criteria
- timed decisions and escalations
- issues found and how they were addressed
- actions, owners and deadlines
- follow-up proof the actions were closed
That’s how you demonstrate readiness beyond box-ticking.
Step 7 — Put the refreshed plan back into a maintenance loop (or it will decay again)
Your maintenance content is blunt: the rate of organisational change drives the rate your plan decays, and a plan that isn’t kept live becomes obsolete.
So your refresh scope should include the “after”:
- top management backing and a visible mandate
- a stable framework (activities, standards, records and controls)
- scheduled and unscheduled activities, scored reviews, and continual improvement
If you don’t bake that in, you’ll be refreshing again in 12 months.
Common gaps a refresh should deliberately look for (quick list)
These are the practical gaps we see most often when reviewing existing BCPs, and they map closely to the issues you highlight across your own material:
- the plan is too long to navigate during a crisis (monolithic)
- runbooks don’t exist per scenario, or aren’t anchored to deadlines
- role responsibilities exist, but aren’t task-focused for the scenario
- exercises are too presentation-like and don’t create urgency or decisions
- contact lists exist but aren’t governed (ownership and cadence missing)
- the plan isn’t integrated across incident, crisis and recovery response
That list is a good “gap assessment checklist” section in the article if you want to make it even more scannable.
Consultant selection checklist (for a BCP refresh)
If you’re bringing in support, this is the shortlist that matters.
Look for consultants who:
- can define scope in a way that’s achievable and tied to recovery deadlines
- will produce scenario runbooks and role cards (not just a big plan)
- design exercises to build capability and generate credible evidence
- actively reduce the time demand on your teams (short, structured sessions)
- can show how they capture lessons and drive continual improvement
Avoid approaches that:
- force a new structure that breaks a previously working, familiar plan just to satisfy an assessor
- treat “exercise completed” as the goal rather than capability and assurance
A practical “BCP refresh” scope of work (example you can lift)
If you want a concrete scope of work you can paste into an internal brief or tender requirement, here’s a good baseline:
- Confirm scope: in-scope services, scenarios, locations and dependencies
- Gap assessment focused on usability and readiness
- Revalidate impact and recovery deadlines, update dependency mapping
- Update runbooks per scenario and align role cards to each runbook
- Refresh contacts and governance (ownership, cadence, access)
- Tabletop exercise (and optionally simulation) to prove the refreshed plan works
- Produce an evidence pack plus prioritised actions backlog
- Put maintenance loop in place to prevent decay
That is refresh work that actually changes readiness.
Closing: the point of a refresh is confidence
Business continuity planning equips you to answer the deluge of questions that appear in a crisis, in relative comfort, and to rebuild while continuing to operate as near-normally as possible.
A refresh that’s worth doing gives you confidence that:
- your response is organised
- your recovery priorities are real
- your runbooks are usable
- your people can execute under pressure
- you can prove it with evidence
That’s readiness. Not box-ticking.